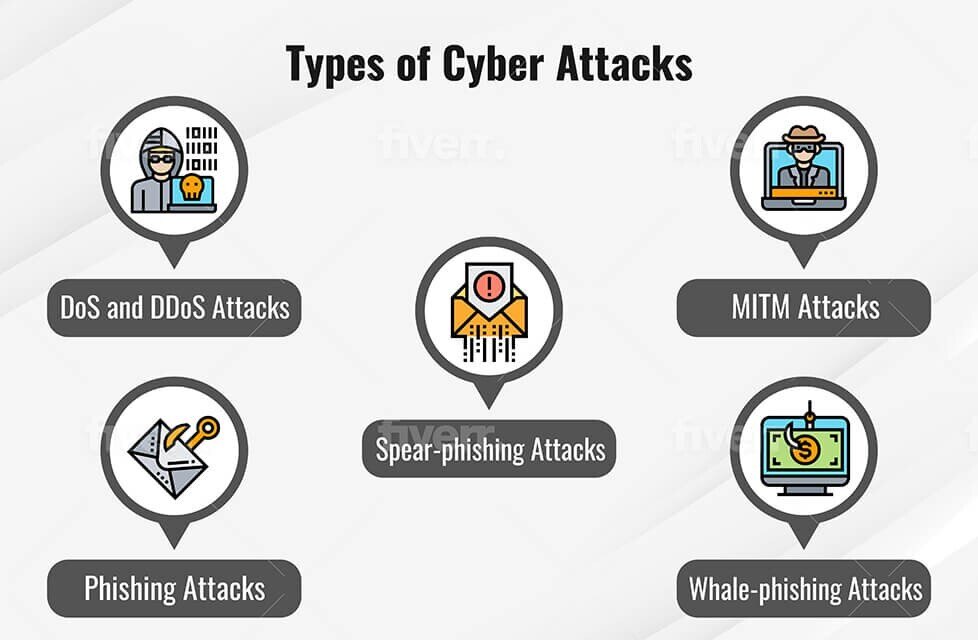
ISC Security Events on Twitter: "#IoT Security Risks! Top 10 #Security targets. Learn more about #CyberSecurity at #ISCEast @SIAonline Education. https://t.co/IcZFkaFfRP" / Twitter
.png)
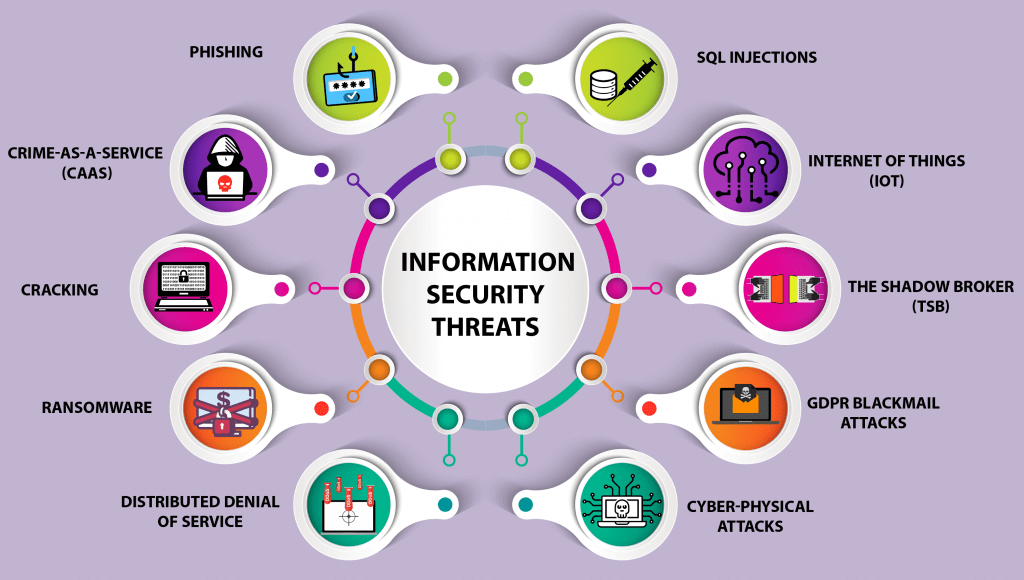
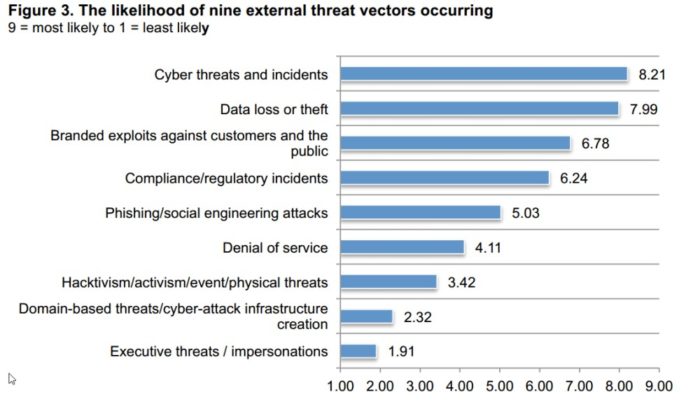
ENISA Threat Landscape 2020: Cyber Attacks Becoming More Sophisticated, Targeted, Widespread and Undetected — ENISA
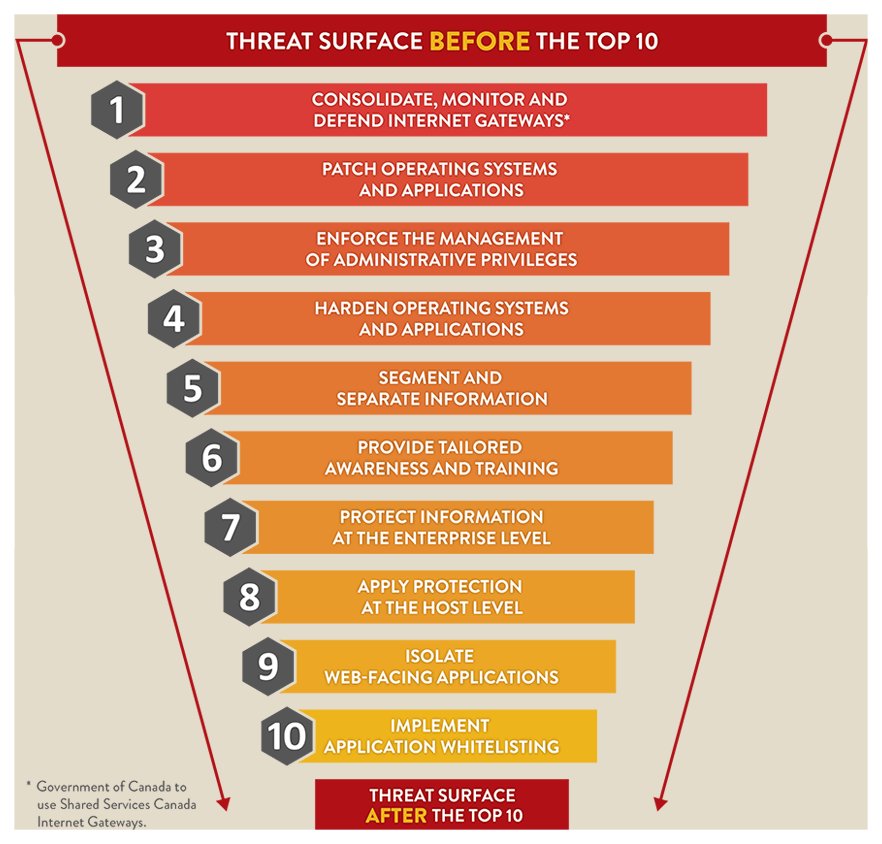
Top 10 IT security actions to protect Internet connected networks and information (ITSM.10.089) - Canadian Centre for Cyber Security